In the modern digital environment, user data has become one of the most valuable assets for any online platform. Every interaction, whether it involves signing up, logging in, or performing financial transactions, generates sensitive information that must be carefully protected. Online platforms that deal with user accounts and financial activity are expected to maintain high levels of trust by ensuring that personal details remain secure from unauthorized access.
Playinexch l are often discussed in terms of how they handle data protection and security architecture. Understanding how such platforms manage security is not only important for users of a specific service but also for anyone interested in how digital safety systems function in general. This article explores the broader mechanisms used in modern platforms to protect user information, with a focus on authentication systems, encryption methods, and monitoring technologies that shape secure digital environments.
The Importance of Digital Security in Online Platforms
The growth of online systems has introduced both convenience and risk. Users now expect fast access to services, but at the same time, they also expect that their personal information will not be exposed or misused. This expectation has led to the development of layered security frameworks that aim to prevent breaches before they occur.
Data security is not limited to preventing hacking attempts. It also includes protecting systems from internal vulnerabilities, accidental data leaks, and unauthorized sharing of information. Platforms operating in competitive digital sectors must therefore build systems that are both flexible and highly secure.
Playin exch operates in an environment where user trust is closely tied to how well data is protected. This makes security design a core part of its infrastructure rather than an optional feature.
Data Encryption as a Core Protection Layer
One of the most fundamental security mechanisms used in digital systems is encryption. Encryption transforms readable data into a coded format that can only be accessed with the correct decryption key. This ensures that even if data is intercepted during transmission, it cannot be easily understood or misused.
Playinexch, encryption is typically applied to sensitive user information such as login credentials, transaction details, and personal account data. Modern encryption protocols often rely on advanced algorithms that are extremely difficult to break without authorized access.
The purpose of encryption is not only to protect stored data but also to secure data during transfer between a user’s device and the platform’s servers. This dual protection ensures that information remains safe at every stage of interaction.
Secure Authentication Systems
Authentication is the process of verifying that a user is who they claim to be. Without strong authentication systems, even the most advanced platforms would remain vulnerable to unauthorized access.
Most modern platforms use multi-layered authentication methods. These may include password-based login systems combined with additional verification steps such as one-time codes or device recognition systems. This ensures that even if a password is compromised, unauthorized users cannot easily access an account.
Playinexch login implements structured login verification processes designed to reduce the risk of unauthorized entry. These systems often rely on secure session tracking, where user activity is monitored from the moment of login until logout. If unusual activity is detected, the system may automatically trigger additional verification steps.
Server Security and Infrastructure Protection
Beyond user-facing security features, the backend infrastructure plays a crucial role in protecting data. Servers that store user information are typically protected through multiple layers of defense, including firewalls, intrusion detection systems, and restricted access controls.
Firewalls act as barriers that filter incoming and outgoing traffic, ensuring that only legitimate requests are processed. Intrusion detection systems continuously monitor server activity to identify suspicious behavior or potential threats.
Playinexch rely on secure server environments to maintain system stability and data integrity. These environments are often designed to isolate sensitive data from public access, reducing the risk of external attacks.
Data Privacy and User Information Handling
Data privacy is another critical aspect of digital security. It refers to how user information is collected, stored, and used by a platform. Responsible systems follow strict data handling policies that limit access to sensitive information and ensure it is not shared without authorization.
In well-structured platforms, user data is stored in encrypted databases with controlled access permissions. Only authorized systems or personnel can interact with specific data sets, reducing the likelihood of misuse.
Playinexch, in line with standard digital practices, is expected to manage user information through structured privacy controls that prioritize confidentiality and controlled access. These mechanisms help ensure that personal data is not exposed beyond its intended use.
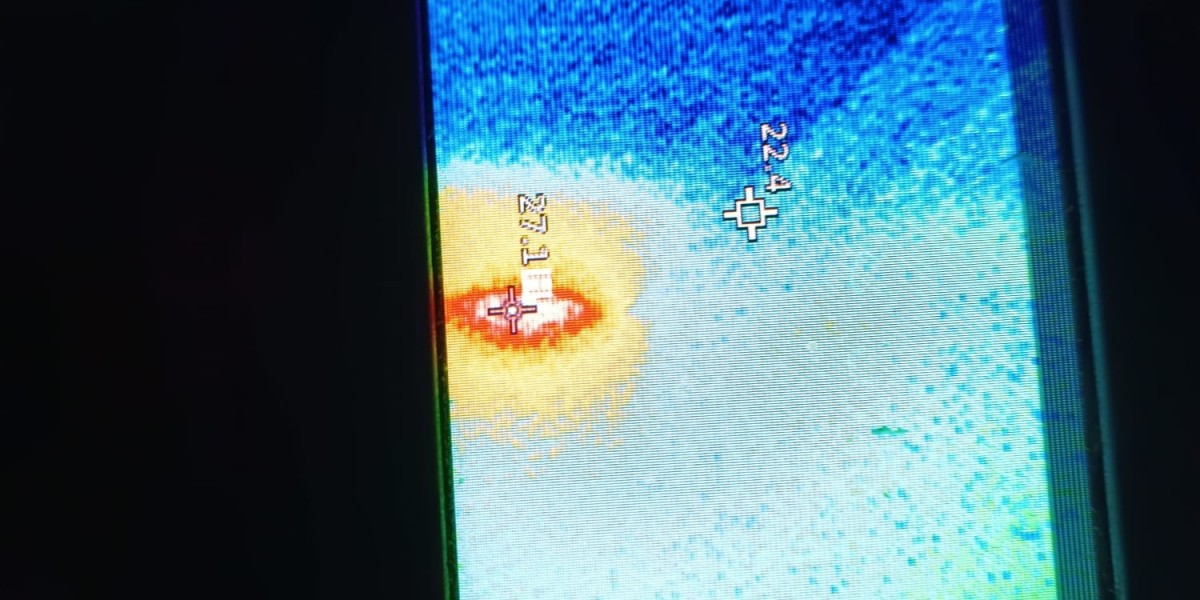
Monitoring Systems and Threat Detection
Continuous monitoring is essential for maintaining platform security. Modern systems use automated tools to detect unusual patterns of behavior that may indicate a security threat.
For example, multiple failed login attempts, unusual location access, or abnormal transaction patterns may trigger alerts within the system. These alerts allow security teams or automated systems to respond quickly before any damage occurs.
Such monitoring systems are not static; they continuously evolve based on new threat patterns and cybersecurity research. This adaptive approach helps platforms stay ahead of potential risks.
Playinexchange incorporates similar monitoring principles to maintain the stability of its digital environment and ensure that suspicious activities are addressed promptly.
Role of Secure Development Practices
Security is not only about protecting a finished system but also about how that system is built. Secure development practices involve writing code in a way that minimizes vulnerabilities from the beginning.
Developers follow guidelines that include input validation, secure API design, and regular vulnerability testing. These practices help reduce the chances of bugs or loopholes that could be exploited later.
Platforms operating in sensitive digital sectors often conduct regular audits to identify weaknesses in their systems. These audits may involve internal testing or external cybersecurity evaluations.
User Responsibility in Maintaining Security
While platforms implement strong security systems, user behavior also plays a significant role in overall safety. Weak passwords, sharing login credentials, or accessing accounts on unsecured devices can increase the risk of data exposure.
Users are encouraged to follow basic digital hygiene practices such as using strong and unique passwords, avoiding public Wi-Fi for sensitive transactions, and regularly updating their login credentials.
Even the most secure platform cannot fully compensate for unsafe user behavior, making awareness an essential part of digital security.
Evolving Nature of Cybersecurity
Cybersecurity is a constantly evolving field. As technology advances, so do the methods used by cybercriminals. This creates a continuous cycle of improvement where security systems must be regularly updated to address new threats.
Modern platforms rely on artificial intelligence, behavioral analysis, and machine learning techniques to enhance their security frameworks. These technologies help detect patterns that may not be visible through traditional monitoring methods.
Playinexch operates in a digital landscape where such evolving technologies are increasingly important for maintaining system integrity and user trust.
Conclusion
Digital security is a complex and multi-layered system that involves encryption, authentication, infrastructure protection, monitoring, and responsible development practices. Platforms that handle user data must continuously adapt to new threats while maintaining user trust through transparent and effective protection methods.
In the case of systems like Playinexch, security is built into multiple layers of operation, ensuring that user information is handled with care and protected through advanced technological frameworks. While no system can guarantee absolute security, the combination of modern cybersecurity practices significantly reduces risks and strengthens overall data protection in the digital environment.